
In this article we will show your how to set up SSH server with Two-Factor Authentication (2FA) for Ubuntu and Debian.
SSH, also known as “Secure Shell“, is a network protocol that can be used to login remote system securely over an unsecured network. You can control your whole server with SSH. So securing SSH is a very important part of any system administrator. By default, SSH uses a password to authenticate the system. You can also use SSH key instead of a password. But, this is only a single factor authentication.
It is always recommended to use Two factor authentication to add an extra layer of security. In two factor authentication, you will need to provide your system user password and another password generated on a mobile device. This will significantly enhance your server’s security.
In this tutorial, we will show you how to secure SSH with two factor authentication.
Requirements
- A server running Ubuntu/Debian with SSH server installed.
- Smart Phone with Google Authenticator installed.
Install and Configure Google Authenticator
In order to set up SSH Server with Two-Factor AuthenticationFirst, you will need to install Google Authenticator PAM module to your system. You can install it by running the following command:
apt-get install libpam-google-authenticator
Once installed, run the Google Authenticator with the following command:
google-authenticator
During the execution, you will need to answer some questions as shown below:
Do you want authentication tokens to be time-based (y/n): y
Warning: pasting the following URL into your browser exposes the OTP secret to Google: https://www.google.com/chart?XXXl=otpauth://totp/root@debian%3Fsecret%3DMSKINXX2OQV54BRLGIJOERK5WE%26issuer%3Ddebian
Press y and hit Enter to continue. You should see a QR code in the following screen:

Next, open Google Authenticator on your Mobile and scan the QR code. Once the QR code is scanned, you should see a six-digit one-time password on your phone:
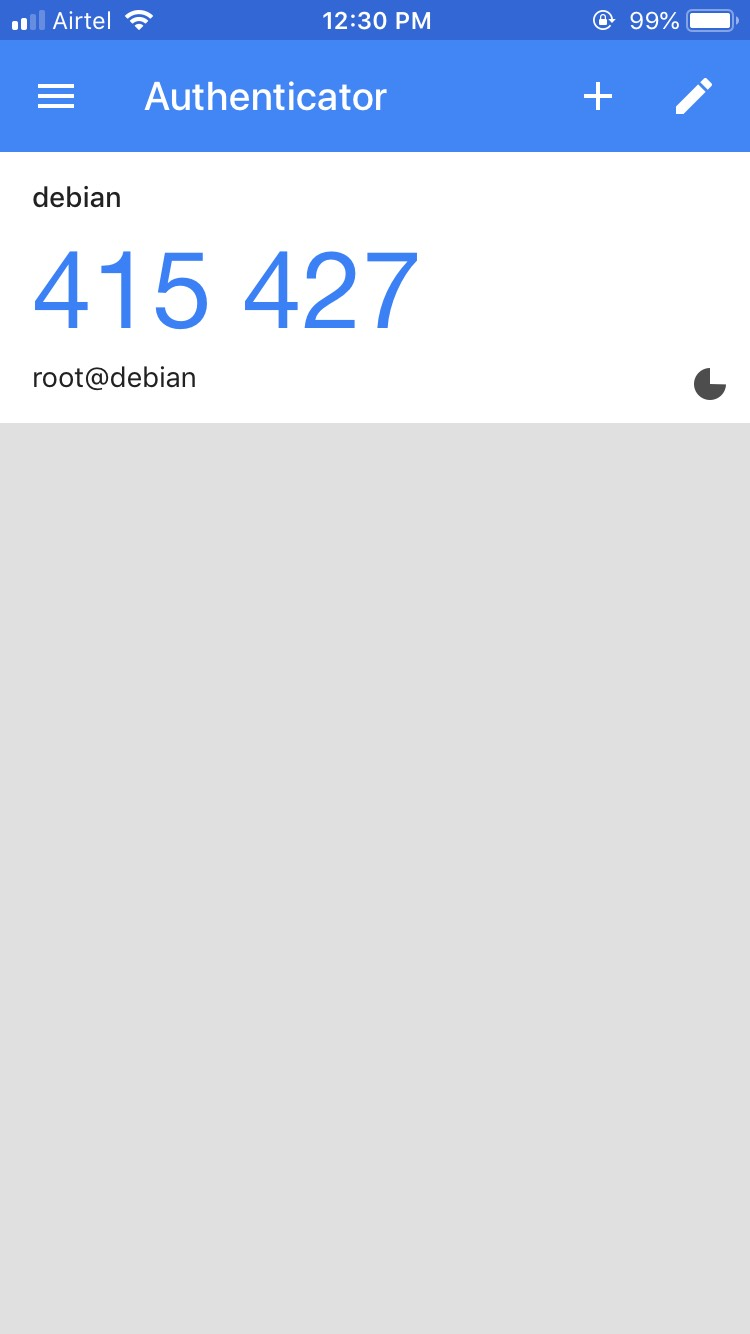
By default, it lasts for 30 seconds. Remember this password, you will need it later in order to log in to Ubuntu server via SSH.
You can also see the secret key, verification code and emergency scratch code in the above output. It is recommended to save it to a safe place for later use.
Next, answer all the questions with y and hit Enter to update your Google Authenticator configuration file as shown below:
Do you want me to update your "/root/.google_authenticator" file? (y/n) y Do you want to disallow multiple uses of the same authentication token? This restricts you to one login about every 30s, but it increases your chances to notice or even prevent man-in-the-middle attacks (y/n) y By default, a new token is generated every 30 seconds by the mobile app. In order to compensate for possible time-skew between the client and the server, we allow an extra token before and after the current time. This allows for a time skew of up to 30 seconds between authentication server and client. If you experience problems with poor time synchronization, you can increase the window from its default size of 3 permitted codes (one previous code, the current code, the next code) to 17 permitted codes (the 8 previous codes, the current code, and the 8 next codes). This will permit for a time skew of up to 4 minutes between client and server. Do you want to do so? (y/n) y If the computer that you are logging into isn't hardened against brute- force login attempts, you can enable rate-limiting for the authentication module. By default, this limits attackers to no more than 3 login attempts every 30s. Do you want to enable rate-limiting? (y/n) y
Configure SSH to Use Google Authenticator
Next, you will also need to configure SSH to use Google Authenticator. You can do it by editing the file /etc/ssh/sshd_config:
nano /etc/ssh/sshd_config
Find and change the following lines to yes:
UsePAM yes ChallengeResponseAuthentication yes
Save and close the file when you are finished. Then, restart SSH service to apply the configuration:
systemctl restart ssh
Next, you will also need to define PAM rules for SSH service in /etc/pam.d/sshd file:
nano /etc/pam.d/sshd
Add the following line after @include common-auth :
auth required pam_google_authenticator.so
Save and close the file.
Test Two Factor Authentication
Your SSH server is now configured with two factor authentication. It’s time to test it.
Log in to another system, open your terminal and connect your server with SSH as shown below:
ssh root@192.168.0.4
You will need to provide your system password and Verification code generate by Google Authenticator.
Password: Verification code:
After successful login, you should see the following output:
Linux debian 4.19.0-5-amd64 #1 SMP Debian 4.19.37-5 (2019-06-19) x86_64 The programs included with the Debian GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Mon Sep 9 01:12:32 2019 from 192.168.0.3
Conclusion
Congratulations! you have successfully set up SSH server with two-factor authentication for Ubuntu and Debian. I hope you have now enough knowledge to protect your SSH server with Google Authenticator.

 Call us at 1-888-GTCOMM1
Call us at 1-888-GTCOMM1





